Grey Hack is a massively multiplayer hacking simulator game.
You're a hacker with full freedom to act as you want on a vast network of computers procedurally created. Each player action influence the world and therefore the other players.
Act for your own benefit, even if it causes collateral damage, help authorities to apprehend criminals or simply keep a low profile and take advantage of the actions of other players.
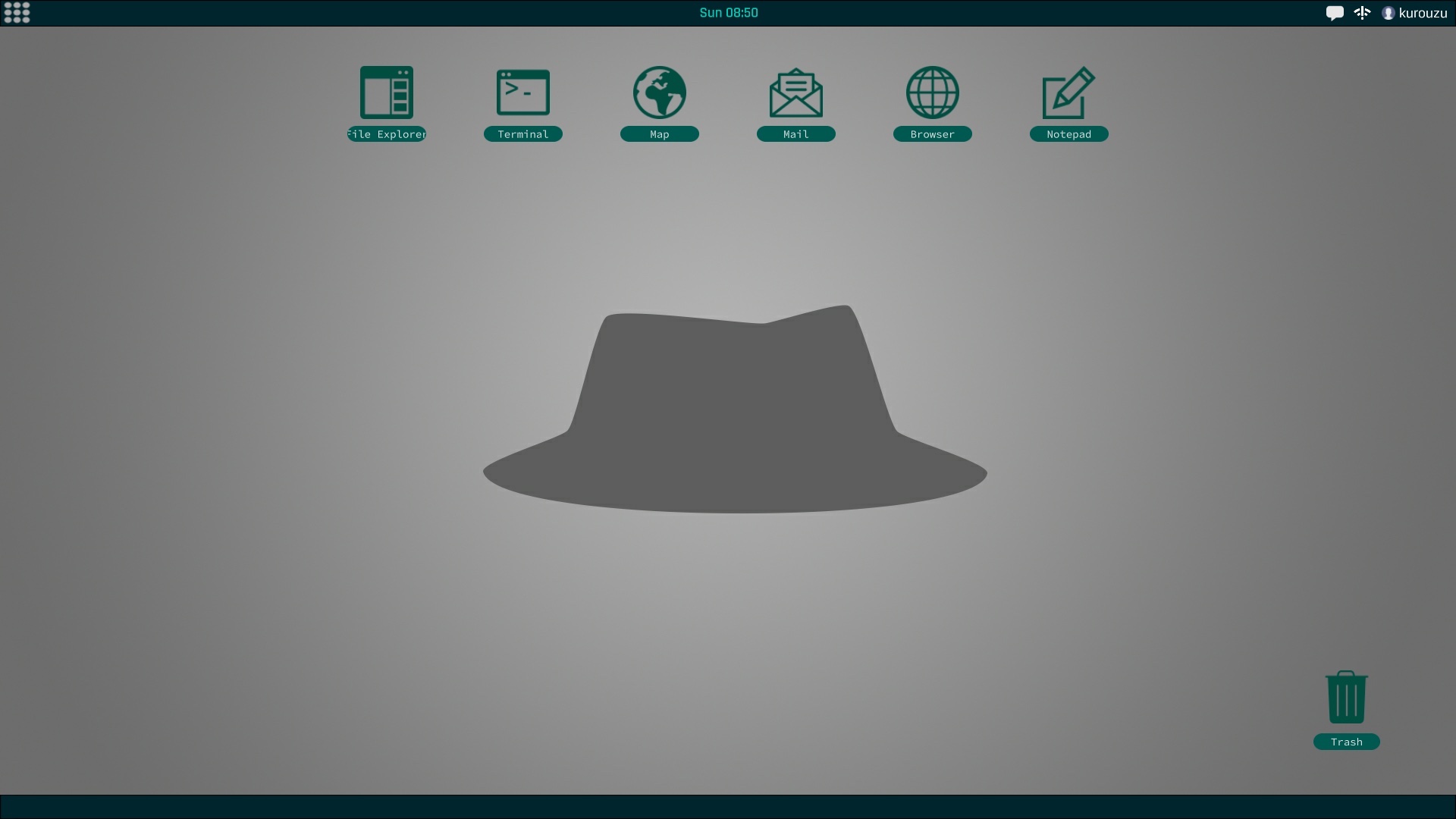
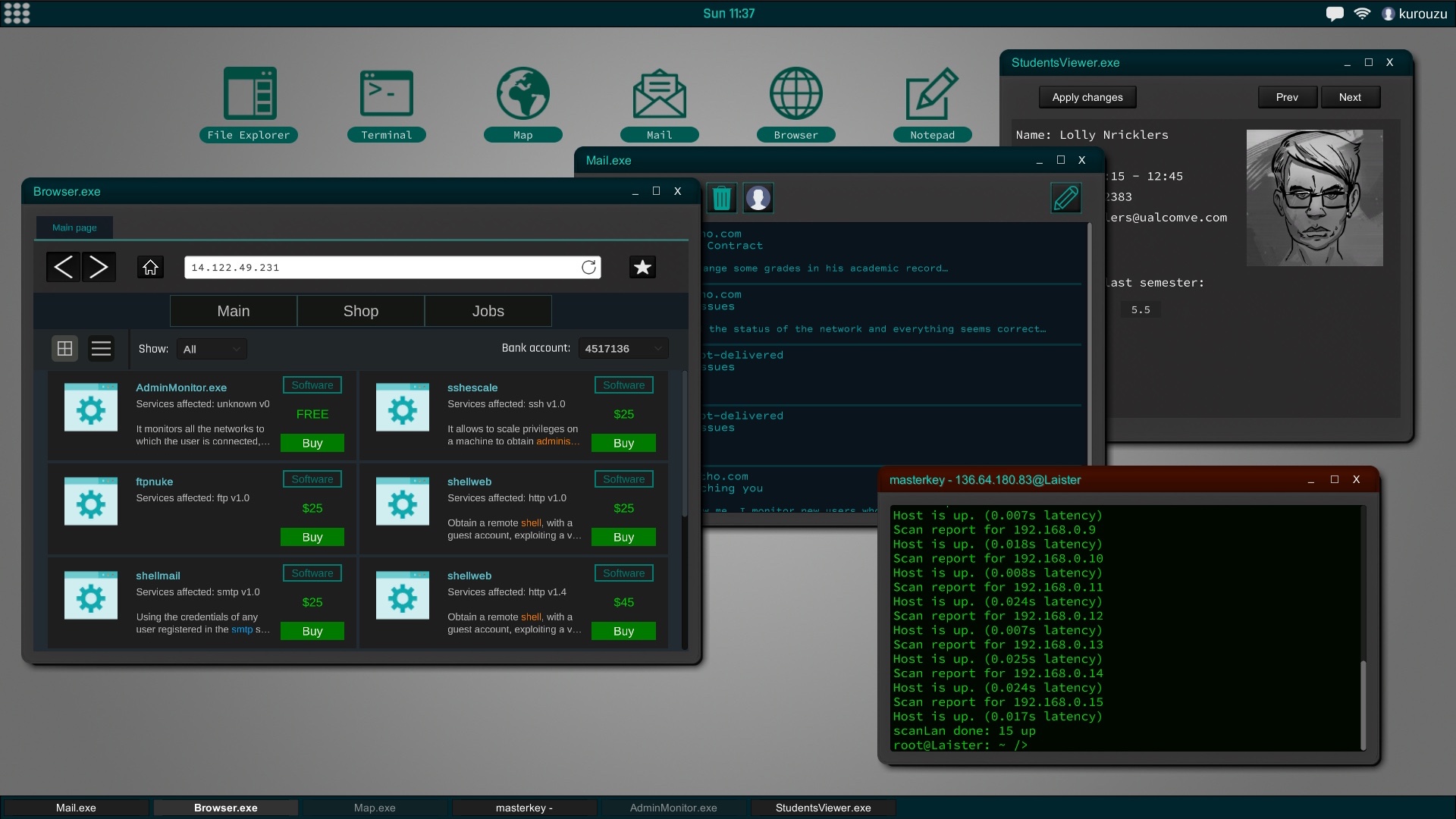
The interface of the game is similar to a current desktop operating system. The file explorer, the command terminal or text editor are some of the programs that will be available from the start of the game. As you improve your skills you will encounter new utilities may install and use.
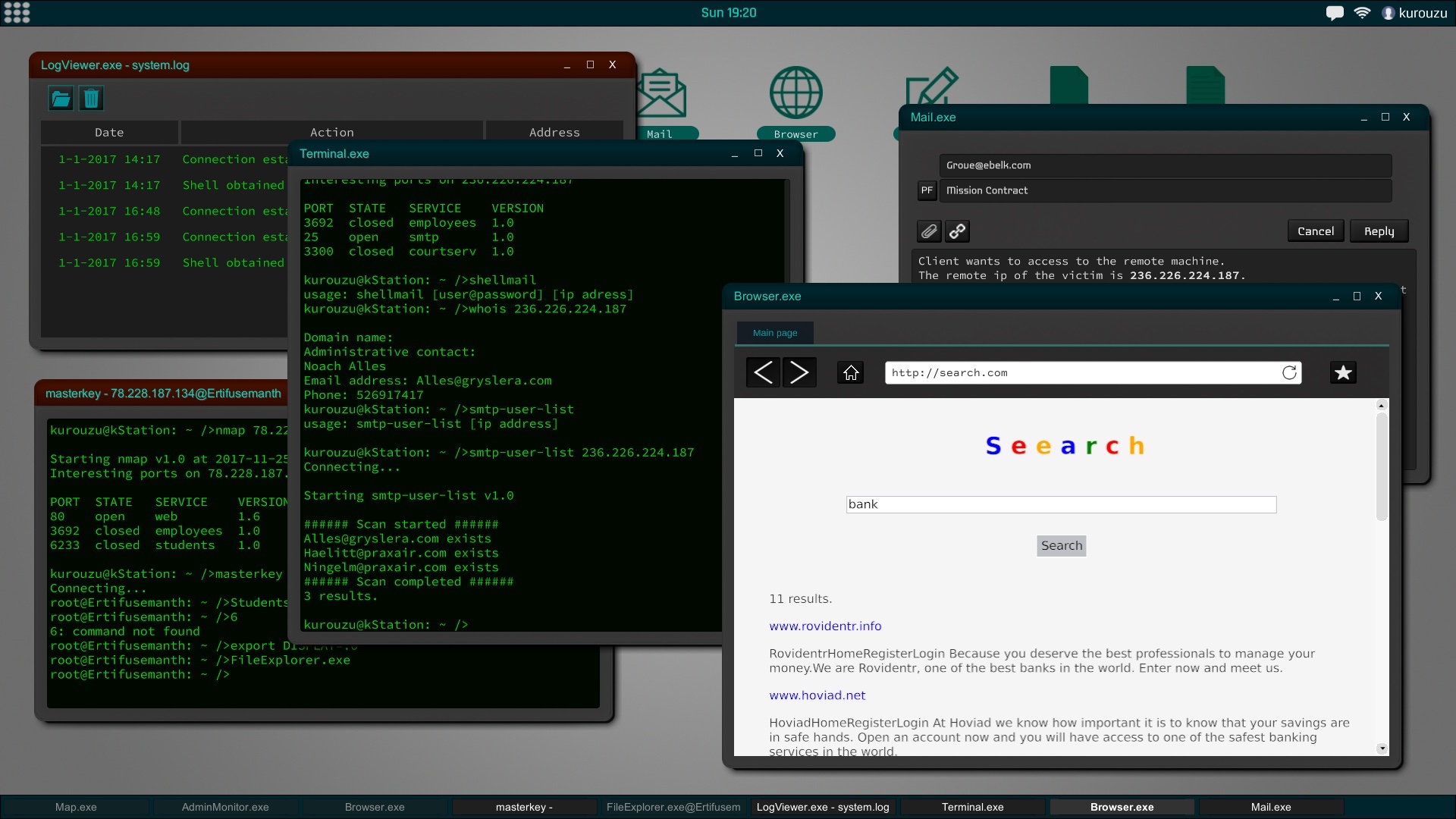
In Grey Hack, terminal has a fundamental role, it is also based on actual unix commands and will be an indispensable tool to perform successfully hacking actions.
When you increase your reputation on the network you can choose to join a group of hackers to carry out coordinated attacks or even create your own. Although if you prefer you can choose to go solo.
Keep in mind that a hacker does not have to act economically, so you decide which missions you accept and if you agree with its consequences.
Social engineering is a powerful tool and, in the most difficult cases, can be very helpful. This means that you can try to trick the user of that computer into giving you their credentials, confidential information about another person, etc.
Going to improve your work station will also be important for more and more professional jobs.
You're a hacker with full freedom to act as you want on a vast network of computers procedurally created. Each player action influence the world and therefore the other players.
Act for your own benefit, even if it causes collateral damage, help authorities to apprehend criminals or simply keep a low profile and take advantage of the actions of other players.
The interface of the game is similar to a current desktop operating system. The file explorer, the command terminal or text editor are some of the programs that will be available from the start of the game. As you improve your skills you will encounter new utilities may install and use.
In Grey Hack, terminal has a fundamental role, it is also based on actual unix commands and will be an indispensable tool to perform successfully hacking actions.
General
Explore the network freely to discover its secrets and missions.When you increase your reputation on the network you can choose to join a group of hackers to carry out coordinated attacks or even create your own. Although if you prefer you can choose to go solo.
Keep in mind that a hacker does not have to act economically, so you decide which missions you accept and if you agree with its consequences.
Network
All computers and networks are generated procedurally to create a new experience in each game. According to the type of network the security will vary to the point of making practically impossible the penetration in certain systems according to the experience and ability that you have.Social engineering is a powerful tool and, in the most difficult cases, can be very helpful. This means that you can try to trick the user of that computer into giving you their credentials, confidential information about another person, etc.
Going to improve your work station will also be important for more and more professional jobs.
World
Each computer in the network is used by at least one user. Each user lives consistently in the world; go to work, shop online, etc. You can impact directly or indirectly in the life of these people in function of what you do.Main Features
- Simulator based on real UNIX commands.
- Operative system UI completely customizable.
- Share the same world with hundreds of players.
- Freedom to choose the type of hacker you want to be.
- Network and world generated procedurally.
- Online data persistence, allowing you to continue later in the same world and with the same computer after leaving the game.
Update v0.7.3590a
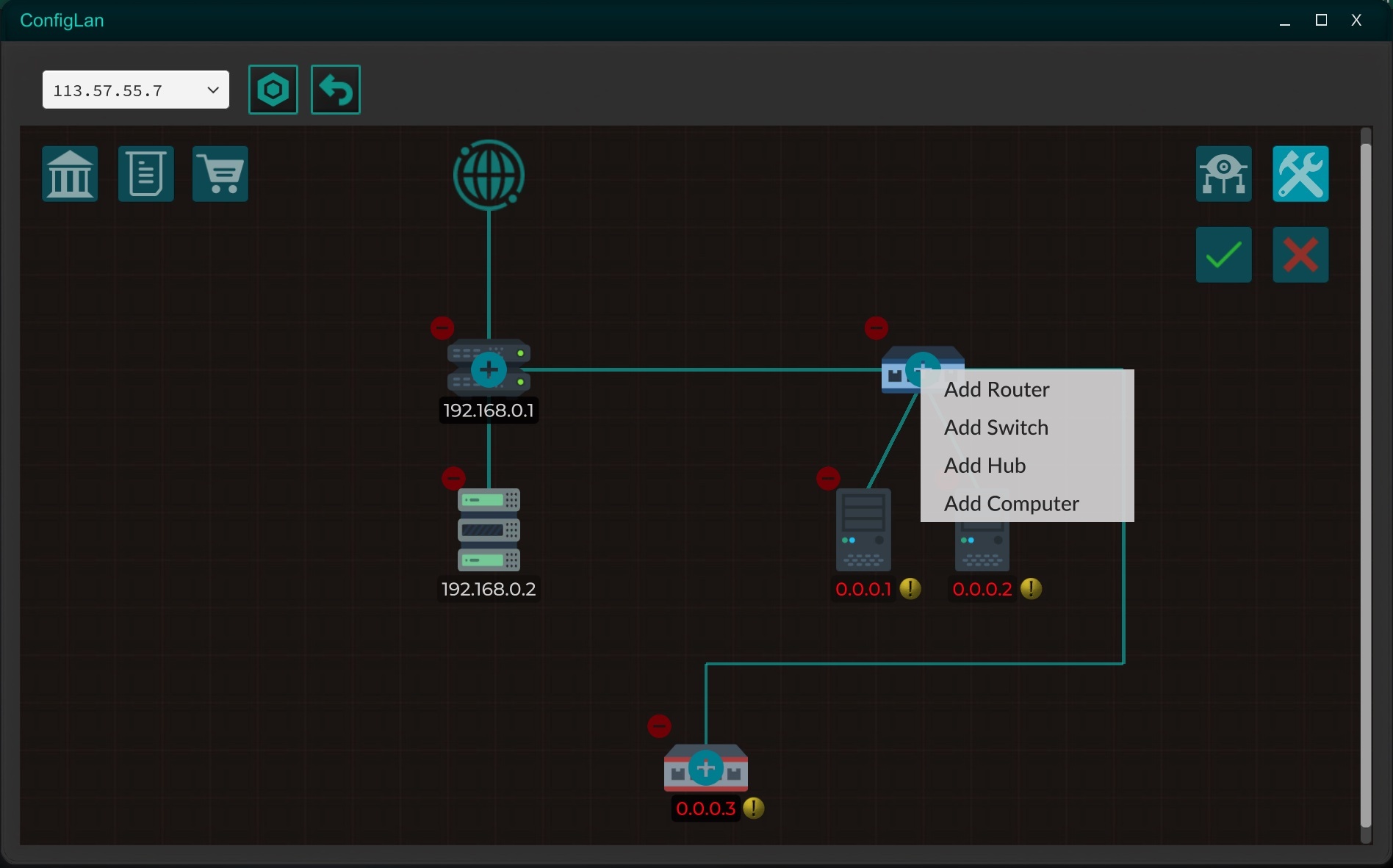
Now rented servers are expanded to rented networks!
By renting a server, new devices can be added to the network, such as routers, switches, hubs or more servers to improve the security of your network, in addition to being able to add firewalls.
With the new ConfigLan tool, you will be able to remotely manage your networks, as well as reset them to their original state if for some reason you have lost the possibility of re-entering the network, either due to a configuration error or a hack.
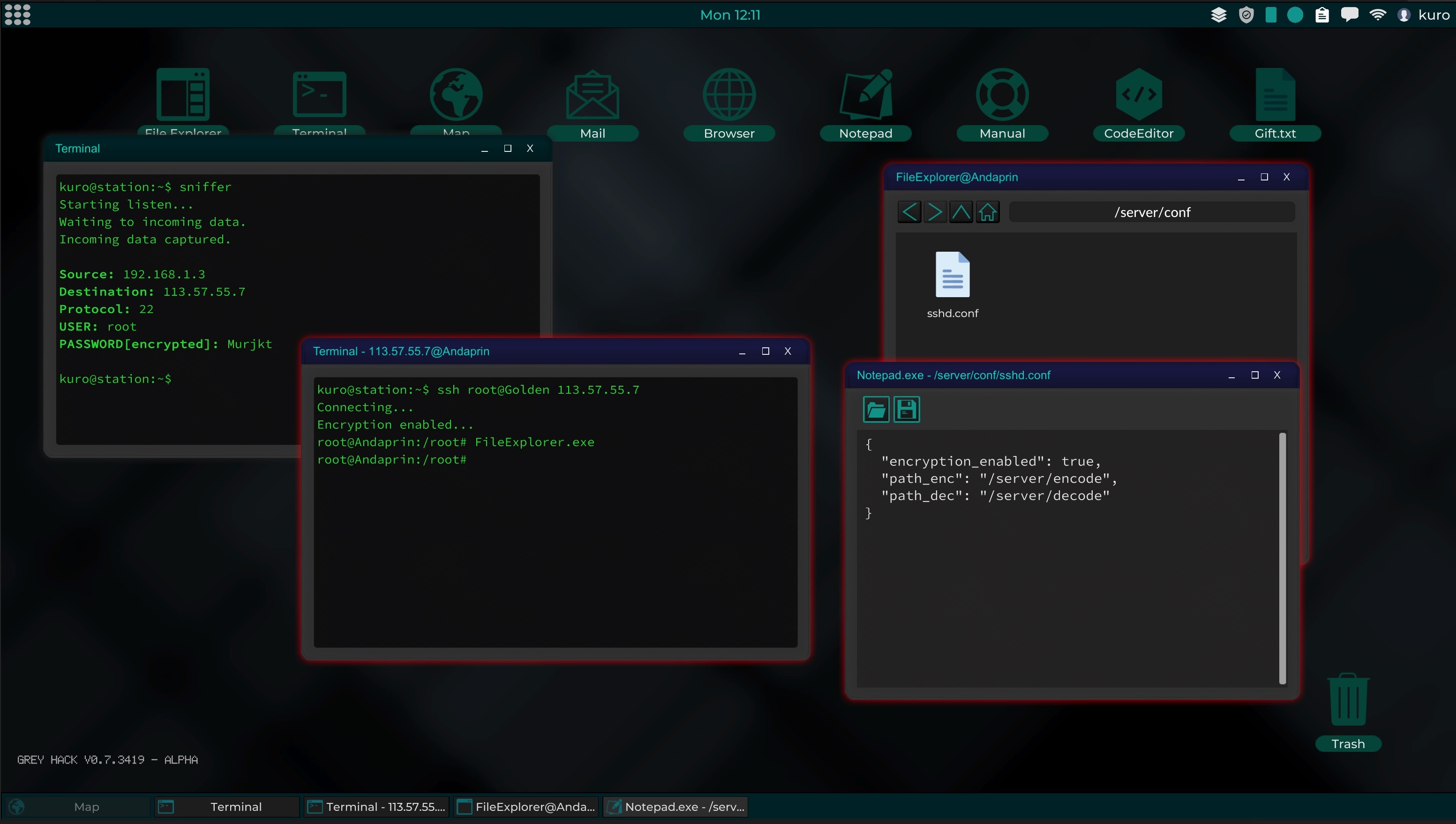
With the introduction of sniffers, players can capture the passwords of npcs and other players.
Now the ssh and ftp services allow an encrypted connection, causing sniffers to only capture encrypted passwords. Although ssh and ftp have a default encryption method, it is easily creackable, since the source code is available for study in the Manual.
Therefore players can program their own encryption system to be used with these services, so that other players can try to crack the encryption system to obtain the password.
This mechanic consist of two scripts that will have to be installed on the server, Encode and Decode. Where sniffers can also capture the source code from Encode, but not from Decode.
As you can imagine, sniffers and encrypted connections will have more prominence in Multiplayer mode than in Single Player mode.

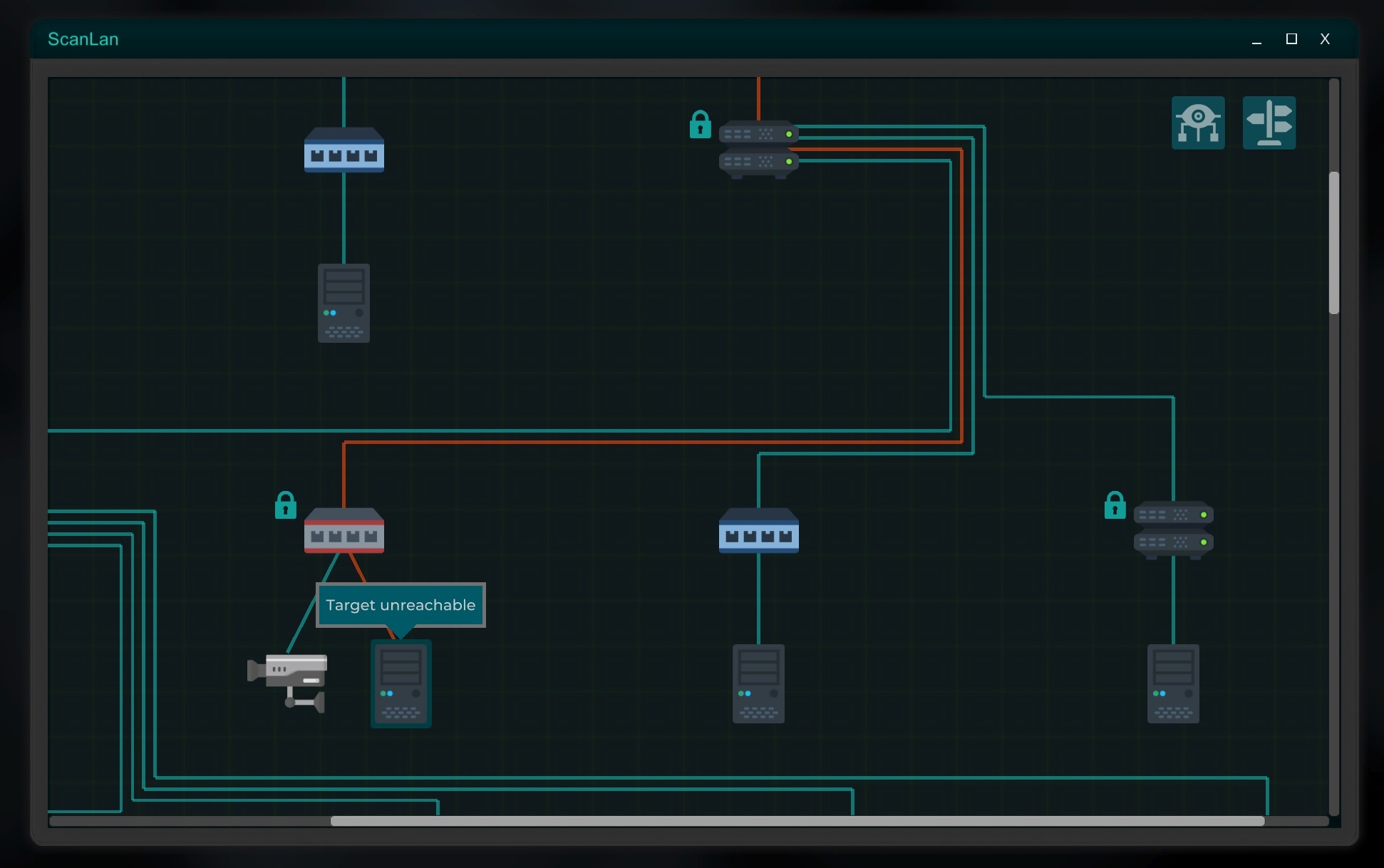
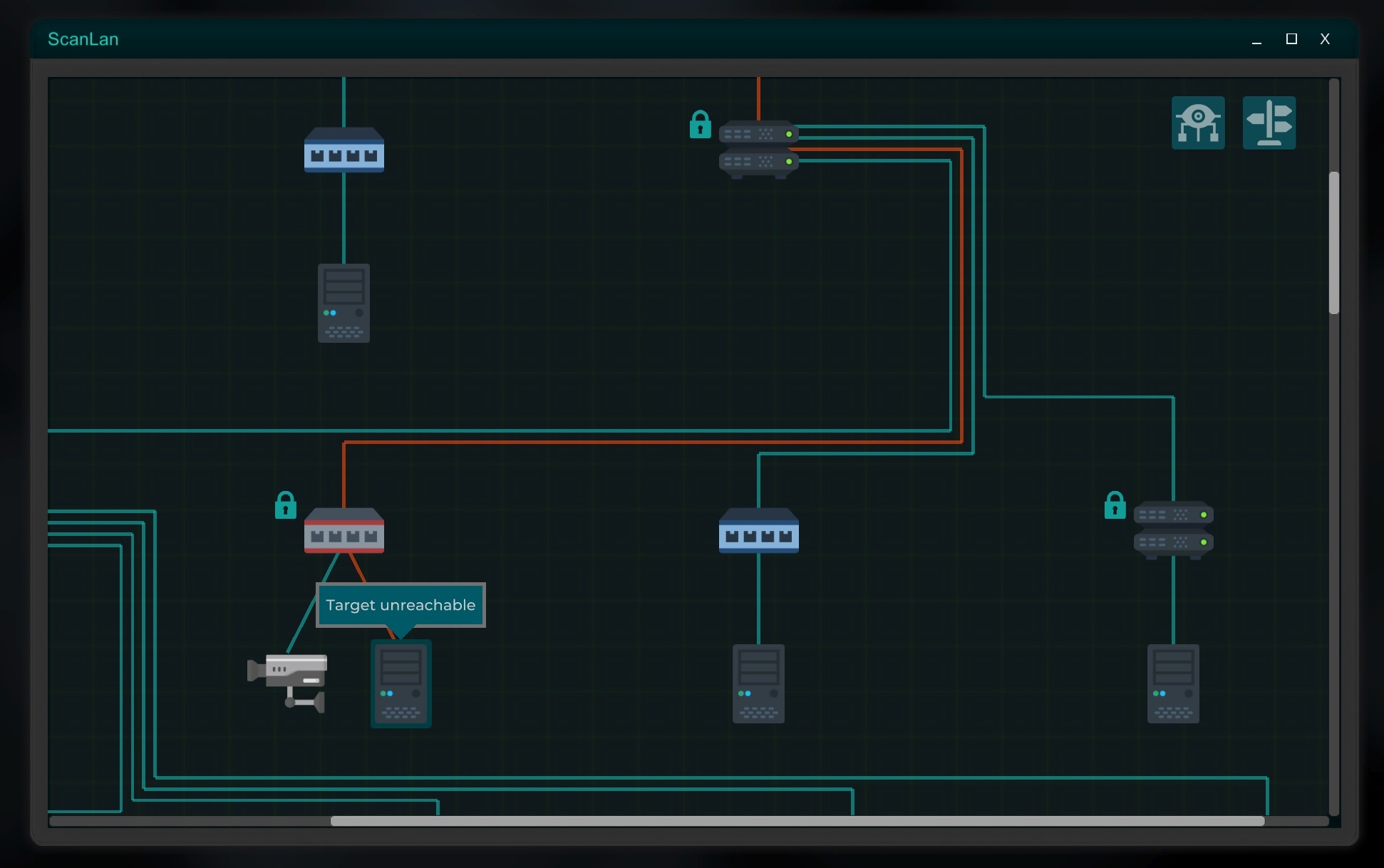
Security cameras have also been implemented, adding one more attack vector.
In some networks you will find security cameras installed, usually in companies, that can show the interior of these buildings. If you look closely at the environment you may find useful information.
The cameras are accessible through the browser, since they use an http server to make the connection, although they require a password to access.
Reverse shells implicitly include the use of a Trojan, since to perform a reverse shell, you must first get the victim to execute your code through social engineering, and this code will install a local service that will connect to your IP as soon as possible, giving you access to a shell.
Keep in mind that you will have to have a publicly accessible service, such as ssh, for this technique to work, making you vulnerable to attacks from others.
Firewalls can be activated on routers, and can be configured to block the entry of traffic through a specific port, or on the contrary allow access to certain IP addresses.
While some versions of kernel_router.so may allow an exploit to disable the firewall, the secure versions will need a bit more work to get through the firewall.
With the new scanrouter tool, which you will be able to find in hackshops, you will be able to scan routers from the outside to know their firewall configuration, in this way you can know which IP addresses are allowed, opening a possible entry to the system when connecting through a machine with a allowed IP.

Improvements have also been added to the interface as well as to the search for content from other players in the internet seach engine, sorting player made web pages by popularity.
In addition to this new features, a significant number of bugs have been fixed. You can check the details in the changelogs of the nightly build prior to this version.
Thanks for your feedback and support!
More news soon!
The public build has been updated with the latest available version of the game!
As usual, since the nightly version becomes the public version, the nightly branch has been closed until the next cycle.
Here is a summary of the main changes and features.
Player custom networks
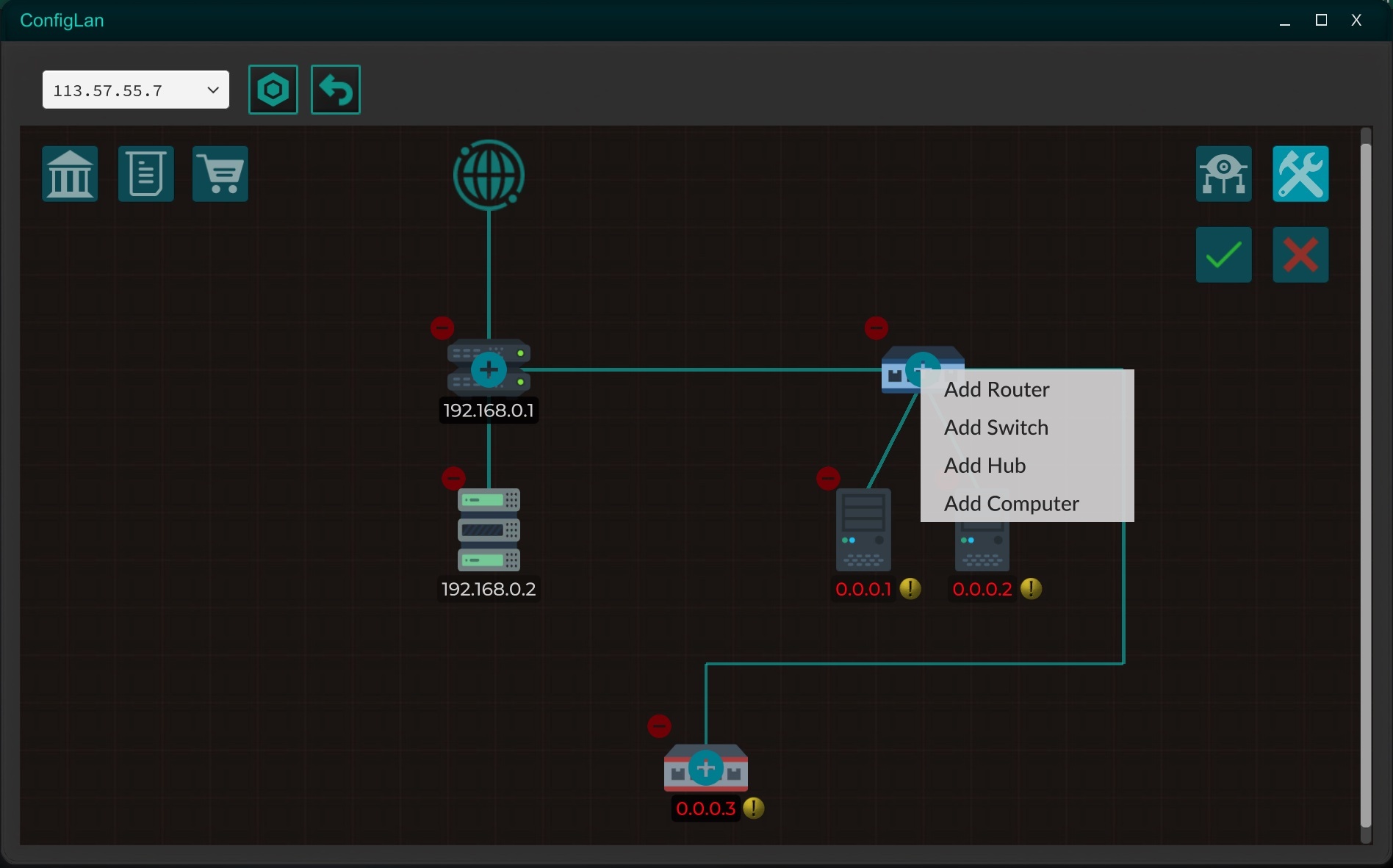
Now rented servers are expanded to rented networks!
By renting a server, new devices can be added to the network, such as routers, switches, hubs or more servers to improve the security of your network, in addition to being able to add firewalls.
With the new ConfigLan tool, you will be able to remotely manage your networks, as well as reset them to their original state if for some reason you have lost the possibility of re-entering the network, either due to a configuration error or a hack.
Sniffers
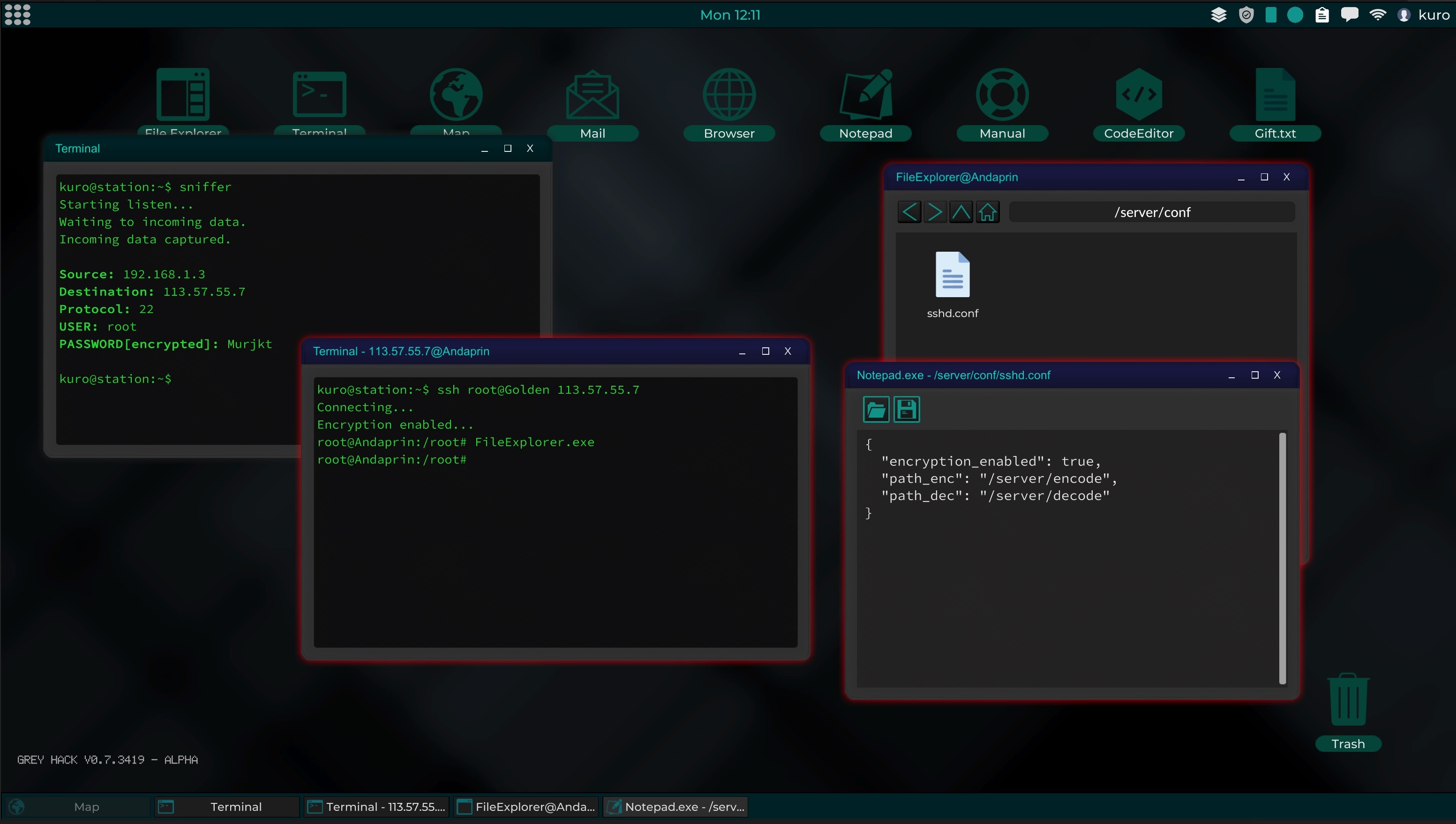
With the introduction of sniffers, players can capture the passwords of npcs and other players.
Now the ssh and ftp services allow an encrypted connection, causing sniffers to only capture encrypted passwords. Although ssh and ftp have a default encryption method, it is easily creackable, since the source code is available for study in the Manual.
Therefore players can program their own encryption system to be used with these services, so that other players can try to crack the encryption system to obtain the password.
This mechanic consist of two scripts that will have to be installed on the server, Encode and Decode. Where sniffers can also capture the source code from Encode, but not from Decode.
As you can imagine, sniffers and encrypted connections will have more prominence in Multiplayer mode than in Single Player mode.
CCTV

Security cameras have also been implemented, adding one more attack vector.
In some networks you will find security cameras installed, usually in companies, that can show the interior of these buildings. If you look closely at the environment you may find useful information.
The cameras are accessible through the browser, since they use an http server to make the connection, although they require a password to access.
Reverse shells
That is, the victim connects to you, instead of you to the victim. This technique allows access to computers that do not have any service installed.Reverse shells implicitly include the use of a Trojan, since to perform a reverse shell, you must first get the victim to execute your code through social engineering, and this code will install a local service that will connect to your IP as soon as possible, giving you access to a shell.
Keep in mind that you will have to have a publicly accessible service, such as ssh, for this technique to work, making you vulnerable to attacks from others.
Firewalls
Firewalls can be activated on routers, and can be configured to block the entry of traffic through a specific port, or on the contrary allow access to certain IP addresses.
While some versions of kernel_router.so may allow an exploit to disable the firewall, the secure versions will need a bit more work to get through the firewall.
With the new scanrouter tool, which you will be able to find in hackshops, you will be able to scan routers from the outside to know their firewall configuration, in this way you can know which IP addresses are allowed, opening a possible entry to the system when connecting through a machine with a allowed IP.
Bug-fixes and other improvements

Improvements have also been added to the interface as well as to the search for content from other players in the internet seach engine, sorting player made web pages by popularity.
In addition to this new features, a significant number of bugs have been fixed. You can check the details in the changelogs of the nightly build prior to this version.
Thanks for your feedback and support!
More news soon!
[ 2021-01-17 02:27:08 CET ] [Original Post]
Minimum Setup
- OS: Ubuntu 18.04. Ubuntu 20.04 and CentOS 7
- Processor: x64 architecture with SSE2 instruction set supportMemory: 512 MB RAM
- Memory: 512 MB RAM
- Graphics: OpenGL 3.2+. Vulkan capable
- Storage: 545 MB available space
GAMEBILLET
[ 6418 ]
FANATICAL
[ 5753 ]
GAMERSGATE
[ 1960 ]
MacGameStore
[ 2357 ]
INDIEGALA
[ 713 ]
LOADED
[ 1040 ]
ENEBA
[ 32767 ]
Green Man Gaming Deals
[ 859 ]
FANATICAL BUNDLES
GMG BUNDLES
HUMBLE BUNDLES
INDIEGALA BUNDLES
by buying games/dlcs from affiliate links you are supporting tuxDB